If your website uses the HTTPS protocol, there’s an important date that you need to remember: June 30, 2018.
Why is that date important? Because that’s when you need to ensure that your website uses one of the more recent encryption protocols.
Specifically, your site should use TLS v1.1 at a minimum. However, it’s strongly encouraged that you use TLS v1.2.
If you’re still using SSL or an older version of TLS at that time, you’ll stand in violation of the PCI Data Security Standard (PCI DSS) for secure payment communications.
Here’s what you need to know about website security and that upcoming deadline.
SSL and TLS
First, it’s good to understand the background of both SSL (Secure Sockets Layer) and TLS (Transport Security Layer).
For practical purposes, you can use both of those acronyms interchangeably. Yes, they are technically different, but when discussing them at a high level (which is what we’re doing here), it’s safe to refer to them as one and the same.
SSL was developed by Netscape (remember that company?) way back in the 1990s. The first version introduced to the public was 2.0.
In an effort to beef up communications security even further, Netscape released v3.0. Unfortunately, though, that version introduced a glaring security vulnerability hilariously named “Poodle.”
After that fiasco, the Internet Engineering Task Force (IETF) moved to adopt the SSL protocol. That motion was granted, and the organization renamed it to TLS.
The first version of the TLS protocol was released in 1999. The latest version is 1.2.
Website Security: How It Works
Webmasters and dotcom companies recognized early on that website security would be important in ecommerce. Without security, how could customers provide their credit card data in confidence?
Enter SSL/TLS encryption. That’s a means of scrambling data transmitted over the wire so that digital eavesdroppers will only see a jumbled mess of characters instead of credit card numbers.
Security protocols also offer confidence that web clients are communicating with trusted servers. They do that with digital certificates.
You can think of digital certificates as high-tech signatures.
Here’s how the whole thing works: when a client connects to a server, the first step is a negotiation. That’s basically a digital handshake.
The negotiation starts by communicating at the highest possible level of security. If that’s not available, then they try lower levels of security until they find one that they can both agree on.
Once they agree on a protocol, secure communication begins.
Old TLS and SSL: Broken Beyond Repair
As we’ve seen, SSL and TLS have evolved throughout the years. Unfortunately, those older versions (SSL v2, SSL v3, and TLS v1.0) are broken beyond repair.
In this case, “broken” means that they’re vulnerable to security threats. And “beyond repair” means that there isn’t any patch available that will fix those older protocol versions.
That’s why you need to ensure that you’re using TLS v1.1 or TLS v1.2 on your website. If you fail to do so, you’re not just breaking a rule set by a standards organization, you’re also jeopardizing customer privacy.
If some hacker exploits the security loophole on your site, they might be able to steal customer data. That will lead to some really bad press.
And, probably, bankruptcy court.
You’re in Need of a Checkup
After reading this, you might be asking yourself the question: “How do I know if my website is compliant with the new standard?”
Unfortunately, there’s not a simple answer to that question.
For starters, if you have a development team that’s familiar with security protocols, you should ask them if your web server is up to snuff. They may have to do some research (that’s okay) but they should be able to tell you in fairly short order.
If you’re running a very small business (or if you’re just a one-person shop) that contracted out your HTTPS setup, you might have to contact your hosting provider. Just call technical support and ask them if your site is using TLS v1.2.
Keep in mind that there’s a good chance that you won’t have to do anything if you’re using a cloud provider. They tend to keep up with all the latest and greatest evolutions in terms of security because they don’t want to lose customers, either.
If you’re running your website on a Windows Server 2012 platform, you can rest easy. That operating system has already disabled the insecure protocols.
On the other hand, if you’re running your website on one of the flavors of UNIX, you’re going to have to do some research. In that case, you’re probably using OpenSSL for website security. You’ll have to check the version of OpenSSL that you’re using and then consult the changelog to see if it supports one of the later protocols.
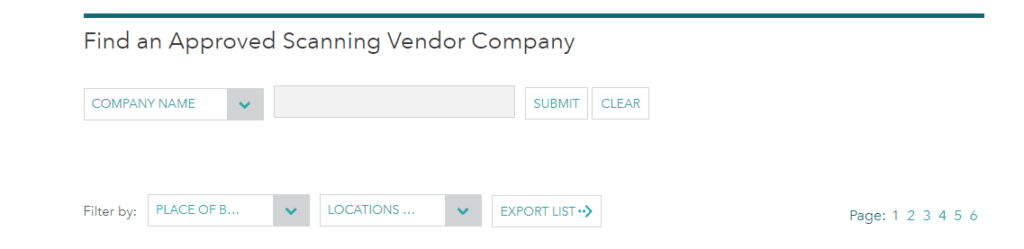
The best thing to do, though, is to get a security audit. You can do that with an Approved Scanning Vendor (ASV).
What’s an ASV? It’s a company with a variety of tools that it uses to check your website security. Specifically, it can make sure you’re compliant with prevailing security standards.
The good news is that the PCI Security Standards Council has a list of approved scanning vendors. The bad news is that it’s going to cost money to use their services.
How much money? That depends on the business and the extent of the scan. Most companies don’t advertise the price on their websites so you can be sure it won’t be cheap.
Keep in mind, though, that many of those ASVs are also companies that specialize in implementing security protocols. Since there are always emerging threats, you should establish a business relationship with one of the vendors and use that company every time you have a need for additional protection.
Search Console Is Your Friend (Again)
Keep in mind that Google Search Console will also alert you if you’re using an older, outdated security protocol.
You may not have seen a notification yet, but now that it’s 2018, you can be sure that you’ll get a warning if you’re not compliant.
How can you check? Just log in to Google Search Console. Take a look at your notifications.
If you see a message that reads: “An outdated version of TLS is being used on the site,” then you need to upgrade. That message could also save you a fortune in ASV charges.
Even better: Google will tell you exactly what you need to do to upgrade your security protocol. Just follow the instructions.
If you’re not much of a technical geek, though, you’ll still probably need to enlist the aid of a developer.
Action Items
If you find that you’re using an old TLS protocol or the SSL protocol on your site, here are the steps you should take:
- Upgrade to TLS v1.1 – At a minimum, you should run TLS v1.1. It’s preferable, though, if you use TLS v1.2.
- Patch TLS – Make sure that your version of TLS is up to date. Hackers are coming up with new ways almost every day to crack even the latest standards. That’s why you should make sure that you don’t just have the latest version, but you have the latest patch.
- Configure TLS – A good bit of web security relies on proper configuration. Ensure that your site supports TLS cipher suites and key sizes.
Above all else, though, you should keep up with the latest news in terms of web security. That way, you can ensure that your website is hardened against threats. It’s a good idea to bookmark a site like ThreatPost.
Of course, that kind of monitoring and implementation takes time away from the mission of growing your business. That’s why you should consider outsourcing the task to a qualified security team.
Remember, though: if you’re using a cloud hosting provider, that company is probably already doing most of that work for you. That is, after all, the whole point of using a cloud hosting provider.
Wrapping It Up
Web security is no small matter. If you fail to take it seriously, you could go out of business. That’s why you should ensure that your website is compliant with the latest security standards.